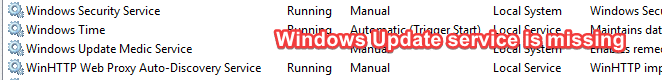
After you restore the missing Windows Update, BITS, or the Update Orchestrator Service services using registry files, you find that the services vanish again after a restart. They don’t appear in the Services MMC.
Cause
This issue happens if your computer is infected. Malware running as a service or scheduled task is deleting the Windows Update (“wuauserv”), Background Intelligent Transfer Service (“BITS”), Update Orchestrator Service (“UsoSvc”), Delivery Optimization (“DoSvc”), and the Windows Update Medic Service (WaasMedicSvc) services at every restart.
For example, a trojan named trojan.Siggen18.38683, which runs as a scheduled task, deletes all the Windows Update-related services at every startup. This is just an example. There may be similar trojans that do this.
How to Resolve the Problem
Step 1: Run a Malwarebytes scan
Download Malwarebytes (https://www.malwarebytes.com/) , update the definitions, and run a full scan.
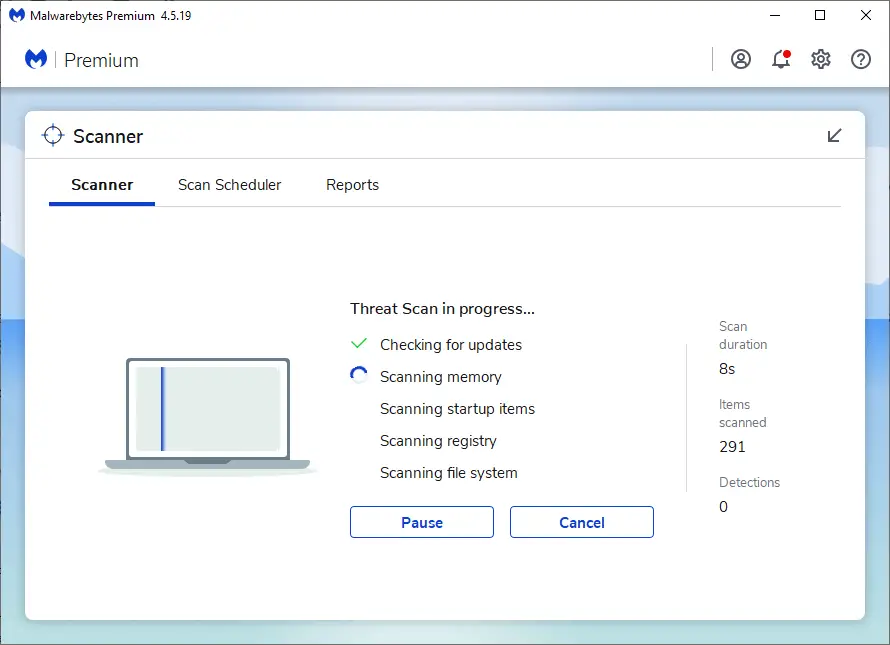
Editor’s note: In a recent case, the trojan “Trojan.Siggen18.38683” seems to have somehow evaded the detection engines of Malwarebytes and Microsoft Defender Antivirus, even though 41 Antivirus vendors (including Malwarebytes and Microsoft) flagged it as malicious. You can read about it in this Microsoft Answers thread.
Step 2: Remove rogue Scheduled Tasks and Services Using Autoruns
After eliminating malware from the computer, download the Autoruns utility from Microsoft, and run the program as administrator.
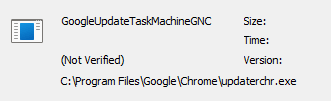
Inspect the Autoruns output thoroughly. In a recent case, we found that the trojan created a fake scheduled task named “GoogleUpdateTaskMachineGNC” or “UpdateTaskMachineQC” that ran one of the following files at every startup.
C:\Program Files\Google\Chrome\updater.exe
%ProgramFiles%\Google\Chrome\updaterchr.exe
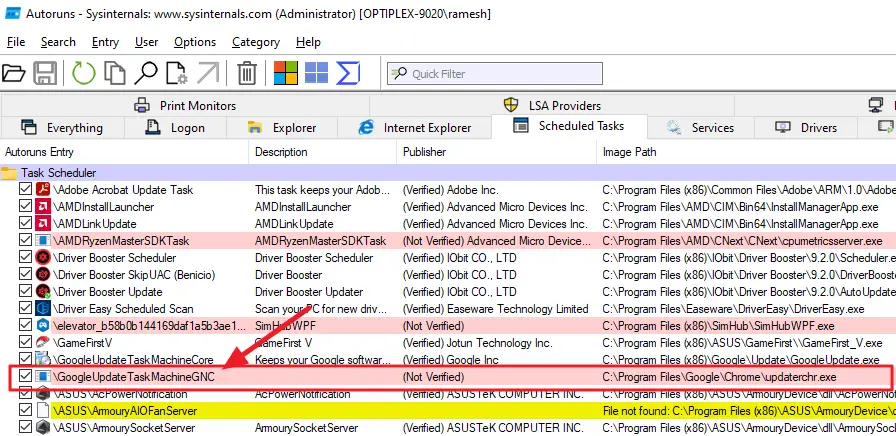
It’s an unsigned/unverified file. Always be suspicious of the “(Not Verified)” entries in Autoruns; Autoruns highlights unverified items in pink. However, it doesn’t mean that the verified entries don’t require scrutiny. Every entry needs to be checked.
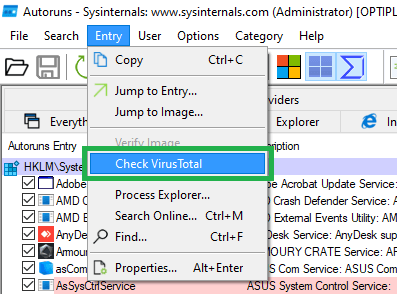
![]() When in doubt, upload the module to VirusTotal to see if it’s malware. Or use Autoruns’s built-in option to upload the file hash to VirusTotal. Select the suspicious item in the list, click the “Entry” menu, and click “Check VirusTotal.” [Ref: Autoruns | Microsoft Press Store]
When in doubt, upload the module to VirusTotal to see if it’s malware. Or use Autoruns’s built-in option to upload the file hash to VirusTotal. Select the suspicious item in the list, click the “Entry” menu, and click “Check VirusTotal.” [Ref: Autoruns | Microsoft Press Store]
Note that the file updaterchr.exe is malware. It hides inside the “Google\Chrome” directory to confuse the user.
After searching the web for the file name and task name, I came across the Dr.Web article. As you can see, the trojan deletes all the services related to Windows Update.
See the VirusTotal report for the file(s).
- VirusTotal – File – updaterchr.exe
- VirusTotal – File – Updater.exe
- Automated Malware Analysis Report – Generated by Joe Sandbox
The trojan also disables the following Microsoft Update scheduled tasks.
"\Microsoft\Windows\UpdateOrchestrator\UpdateAssistantWakeupRun" "\Microsoft\Windows\WindowsUpdate\Automatic App Update" "\Microsoft\Windows\WindowsUpdate\Scheduled Start" "\Microsoft\Windows\WindowsUpdate\sih" "\Microsoft\Windows\WindowsUpdate\sihboot" "\Microsoft\Windows\UpdateOrchestrator\UpdateAssistant" "\Microsoft\Windows\UpdateOrchestrator\UpdateAssistantCalendarRun"
It deletes the following Windows Update service registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\UsoSvc HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\WaaSMedicSvc HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\wuauserv HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\bits HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\dosvc
Deleting the task “GoogleUpdateTaskMachineGNC” and the rogue file resolved the problem.
Note: Your system may have a *different* kind of malware and in a different startup entry point (not necessarily a scheduled task). The above was provided as an example.
Realtek Audio Updater (Fake)
On another system, a fake Realtek Audio Updater program (updater.exe) caused the issue. The rogue module usually exists in the following folder:
C:\Program Files\Realtek\Realtek High Definition Audio\Updater.exe
And it’s configured to run as a scheduled task with the highest privileges.
System32\Tasks\Realtek => C:\Program Files\Realtek\Realtek High Definition Audio\Updater.exe
At every startup, the rogue Updater.exe process deletes your Windows Update-related services.
Fake Driver Updater
In another case, a fake Driver Updater caused the issue. The rogue task deleted the WU-related services whenever it was run.
System32\Tasks\DriverSetup => C:\Program Files\DriverSetup\Driver\DriverSetup.exe
VirusTotal – File – DriverSetup.exe.
Step 3: Reset Windows Security “Exclusions”
The above virus creates some exclusions in Windows Security. After cleaning up the entries, open Windows Security and remove these folders from the list of “Exclusions”:
- C:\Users\{username}
- C:\Program Files
To reset the exclusions en masse, see the article How to Bulk Reset Exclusions in Windows Defender.
Step 4: Restore the missing Windows Update Services
The last step will be to restore the missing services. After importing the registry files mentioned in the following articles, the system requires a reboot for the changes to take effect.
- Restore the missing Windows Update (wuauserv) Service
- Restore the missing BITS Service
- Restore the missing “Update Orchestrator Service”
- Restore Missing Delivery Optimization Service (DoSvc)
It’s crucial to eliminate the viruses from the computer before recreating the Windows Update/BITS/UsoSvc/DoSvc/WaasMedicSvc service registry keys.
One small request: If you liked this post, please share this?
One "tiny" share from you would seriously help a lot with the growth of this blog. Some great suggestions:- Pin it!
- Share it to your favorite blog + Facebook, Reddit
- Tweet it!