When you run a Windows script using wscript.exe or cscript.exe, error Windows Script Host access is disabled on this machine may pop-up. However, in systems affected by malware, the error appears at regular intervals, without any script invocation by the user.
So the key questions are:
- Which script is being run that causes the error message?
- How do I enable Windows Script Host access in the machine?
This post address those questions.
Contents
[Fix] Windows Script Host Access is Disabled on this Machine
If the message “Windows Script Host access is disabled” appears at every startup or in regular intervals without you doing anything, then a malware script (.vbs, .js or .wsf) may be trying to run in the background, and is prevented by Windows Script Host restriction in effect in your system, which is very good. In such cases, your aim should be to eliminate the malware from the system completely rather than fixing the script host error message.
Run a thorough malware scan in your system first. Until every trace of malware is removed, do not lift the script host restriction. The restriction is only protecting your system.
Investigate which script is trying to run that causes the error?
If the error appears without you manually launching a script, then it’s possible that a malware script is trying to run in the background, probably as a scheduled task.
Use Task Manager to find the script file name
You can use a simple tool like Task Manager to find out the script file name that’s being executed. Use these steps:
- Let the script error window be on the screen. Don’t dismiss it yet.
- Disconnect your computer from the internet.
- Open Task Manager (Ctrl + Shift + Esc) and click the Details tab.
- Right-click the column header, click Select Columns.
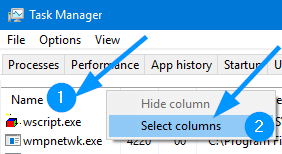
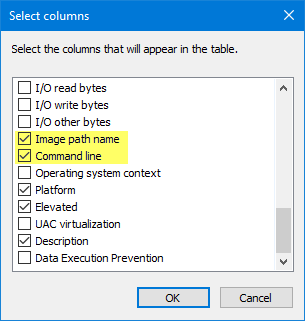
- Enable the Command line checkbox and click OK.
RELATED: Check out post Configure Task Manager to display full path of running processes for more information and screenshots.
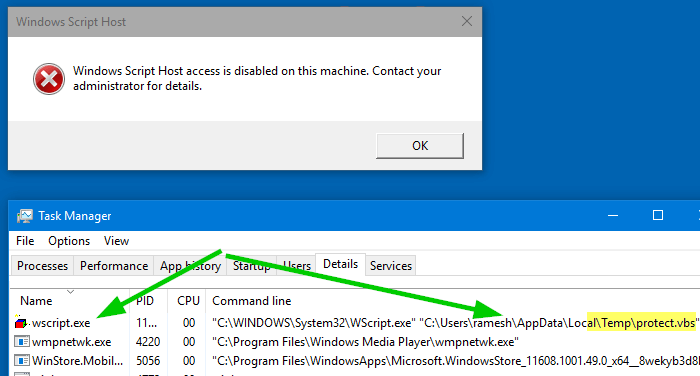
This shows the complete path and file name of the script file which is trying to run silently. In this example, a script file named protect.vbs is trying to run from the %TEMP% folder of the user profile.
Related: Process Explorer from Windows SysInternals can be used to find the process name, path and full arguments. Check out post How to Find Which Program Caused An Unknown Error Message? for details.
Use Advanced Troubleshooting Tools
Further, you can use Autoruns, another excellent tool from Microsoft Windows SysInternals to find the startup launch-point (Startup or Task Scheduler) used by that malware script.
Start your investigation from there. If you’re an advanced user, you can even edit the script file using Notepad and see what code is being executed. Ransomware usually employs .vbs, .js, .wsh or .hta files to download the crypto-ransomware payload from a remote server, run it on your local system and encrypt your data or erase them completely.
First of all, if someone could drop a malware script in your TEMP directory and launch it, then there exists some really serious vulnerability in your system. Antivirus and anti-malware protection may not always help if your system is vulnerable to an exploit. You should make sure that your system is up to date in terms of Windows Update patches, as well as updates for the programs you’re using in your system.
Do a thorough checkup using a reputed anti-malware tool such as Malwarebytes.
How do I enable Windows Script Host access?
If your system is not connected to a domain, here are the steps to remove the error “Windows Script Host Access is Disabled”. This procedure will enable running Windows Scripts (.vbs or .js) on your system.
Enable Windows Script Host access using the Registry Editor
- Press WinKey + R to bring up the Run dialog.
- Type
regedit.exe - Delete the value named Enabled in following keys:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings
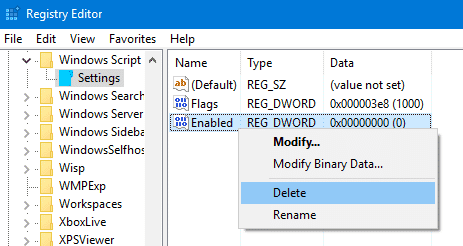
If a key doesn’t exist, ignore and check the next key. - Exit the Registry Editor.
Enable Windows Script Host access using command-line
To do this using command-line, execute these commands from elevated Command Prompt:
REG DELETE "HKCU\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled /f REG DELETE "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled /f
With the Windows Script Host restrictions lifted, you should only run scripts from trusted sources and if you’re sure they are safe to run.
That’s it! This enables Windows Scripting host on your computer.
One small request: If you liked this post, please share this?
One "tiny" share from you would seriously help a lot with the growth of this blog. Some great suggestions:- Pin it!
- Share it to your favorite blog + Facebook, Reddit
- Tweet it!
for many period of time pc saying window script host is disabled on this machine. for the error i tried to sove many time but i can’t. would like to help me why this problem is happened and how can i solve this problem. and also would you tell me the use of this script. for your help i say thanks.From bilisumma!
My hp notebook the same message after pressing ok it then shows a blank screen…how can I fix this problem.
Thanks so much! Nobody else made any sense.
REG DELETE “HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings” /v Enabled /f
after executing this in cmd .. the output was access denied
You need to run that command from elevated Command Prompt.
Thank You so much for the help
Innocent Shange I am experiencing the same issue, to remove blank screen, press Ctrl+Alt+Del, go to task manager, file, new task, then type “explorer.exe”. This should bring up your windows explorer. N.B You will have to do this upon every restart, until you enable it in the registry
i am experiencing this problem.. should i update my anti-virus and do a full scan to solve this..?? considering the fact that apparently it is caused by a malware disabling the script host
WSH disabled is a good thing. Investigate what’s trying to run in background, though.
I have tried the steps with windows 8.1 but it is not working still.
How do I go about fixing this problem on a windows 8.1 OS?
This is helping I can see my icons now.
Good day! Thanks for this, but what if the home screen is just in a black out mode, I can only see the cursor, what would be the solution for this? Thanks.
@ynna: Tried this? https://www.winhelponline.com/blog/cannot-find-script-run-vbs-logon/
Tanx a lot
It really worked
#Reaper ….thanks so much, its really works
My window could not open when I open my window the Host bar showed
I’m facing this issue and its starting to get on my nerves as I can’t run driverspack solution, I’m using windows 8.1 by the way. My problem is that there is no “Enabled” file or button to click on in the settings folder of the Windows Script Host. Can someone please help me work this out asap.
Thanks in advance
Thank you first of all, i tried from so many sources to enable script host but no one has worked out, but your trick has worked.
I follow your steps but still it give me back that message!
Thank you very very very much it worked
i hv issue with windows script host, but after changing it following the process, its still given the same response saying “enable your window script host, pls help on this
@Awoniyi : Have you checked both registry keys (under HKCU and HKLM)?
This is what I did and it worked. Thank you so much. Other websites only talked about HKLM.
If I have deleted the enable option in script host setting, how can I get it back when later on I need it?
If you need the value back, you can create a new one (of type DWORD 32-bit)
Thanks a lot brother. This article has helped me resolve the windows script host issue and I have been able to activate my MS Word 2016 successfully.
Thanks a lot.
Thank you so very very much
Thank you so much
Wow thank u a lot🙏 the command has just worked on my windows 7 ultimate. Wanted to prolong time required to activate since i got it online. As am looking forward to fully activate it. Thanks thanks for the good work
I have managed to resolve the “Windows script host access disabled” error by following the procedure displayed on your page. I deleted the the registry line as you advised.
It worked well for me. I am now able to install the software.
Thank you so much!!! I am grateful for you help.
There is no need to delete it just update it’s value from 0 to 1
0 = Disabled
1 = Enabled
Than you sooo much i’ve been having this problem for weeks. I’m so glad it worked
thanks<3
I did all of the mentioned instructions but still could not run the scriot to install the driver to my USB wifi dongle, until I noticed a notification in the try stating that the anti malware / antivirus app is actually blocking the script from running. I’d disable the protection for a while before trying other steps that may appear to be a bit technical to noobs.Thank you..just my10cent of contribution, hoped it helps
thanks, your method works
Thank you very much my system is working perfectly fine.