When you open the Security Event log, the log may contain many “Filtering Platform Connection” events. The event ID of these entries maybe 5156 or 5158. The security log may record close to 100 events per minute, containing the event ID 5156 or 5158. This causes the security event log to become full very quickly.
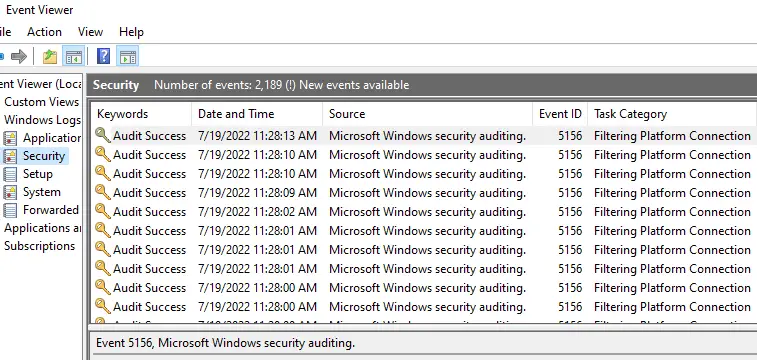
Sample Event ID 5156 entry
Log Name: Security Source: Microsoft-Windows-Security-Auditing Date: 7/19/2022 11:27:37 AM Event ID: 5156 Task Category: Filtering Platform Connection Level: Information Keywords: Audit Success User: N/A Computer: OptiPlex-9020 Description: The Windows Filtering Platform has permitted a connection. Application Information: Process ID: 2592 Application Name: \device\harddiskvolume2\program files (x86)\microsoft\edge\application\msedge.exe Network Information: Direction: Outbound Source Address: 192.168.0.101 Source Port: 63386 Destination Address: 239.255.255.250 Destination Port: 1900 Protocol: 17 Filter Information: Filter Run-Time ID: 144025 Layer Name: Connect Layer Run-Time ID: 48
Sample Event ID 5158 entry
Log Name: Security Source: Microsoft-Windows-Security-Auditing Date: 7/19/2022 11:27:51 AM Event ID: 5158 Task Category: Filtering Platform Connection Level: Information Keywords: Audit Success User: N/A Computer: OptiPlex-9020 Description: The Windows Filtering Platform has permitted a bind to a local port. Application Information: Process ID: 7612 Application Name: \device\harddiskvolume2\program files (x86)\google\chrome\application\chrome.exe Network Information: Source Address: :: Source Port: 60420 Protocol: 17 Filter Information: Filter Run-Time ID: 145279 Layer Name: Resource Assignment Layer Run-Time ID: 38
The security event log getting bombarded with 100 events per minute is never a good thing. Not only it’s an unnecessary disk I/O operation, but it also FIFOs out other vital security log data.
Cause
Windows Filtering Platform (WFP) is a set of API and system services that provide a platform for creating network filtering applications. Windows Firewall is based on WFP.
On a standard Windows installation, the Success/Failure entries for “Filtering Platform Connection” aren’t audited/logged. However, third-party software may have enabled auditing for this category. If auditing is enabled, Windows Filtering Platform generates the events 5156 and 5158 when it has allowed a connection. Event ID 5157 is written when WFP has blocked a connection.
For more information on WFP auditing, see this Microsoft article.
This article tells you how to prevent a spate of “Filtering Platform Connection” events from being written to the Security event Log every minute.
Solution
To stop Windows Filtering Platform from (“Filtering Platform Connection”) from logging Success and Failure events (5156, 5157, and 5158) in the Security event log, follow these steps:
Disable “Filtering Platform Connection” Success Audit
First, open an admin Command Prompt.
Type the following command and press Enter:
auditpol /set /subcategory:"{0CCE9226-69AE-11D9-BED3-505054503030}" /success:disable /failure:disable
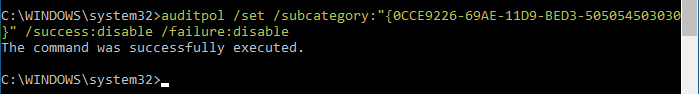
That’s it. The Security event log should no longer get bombarded with events 5156, 5157, or 5158 from now on.
auditpol /get /subcategory:"{0CCE9226-69AE-11D9-BED3-505054503030}"
You should see the following output:
System audit policy Category/Subcategory Setting Object Access Filtering Platform Connection No Auditing
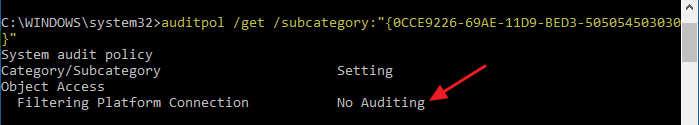
The above output means auditing is disabled (for both “Success” and “Failure” WFP events) and nothing will be logged. This is what we wanted.
The security event log will have recorded the following event after the audit policy change:
Log Name: Security
Source: Microsoft-Windows-Security-Auditing
Date: 7/19/2022 12:50:01 PM
Event ID: 4719
Task Category: Audit Policy Change
Level: Information
Keywords: Audit Success
User: N/A
Computer: OptiPlex-9020
Description:
System audit policy was changed.
Subject:
Security ID: OPTIPLEX-9020\ramesh
Account Name: ramesh
Account Domain: OPTIPLEX-9020
Logon ID: 0x92A6F
Audit Policy Change:
Category: Object Access
Subcategory: Filtering Platform Connection
Subcategory GUID: {0cce9226-69ae-11d9-bed3-505054503030}
Changes: Success removed, Failure removed
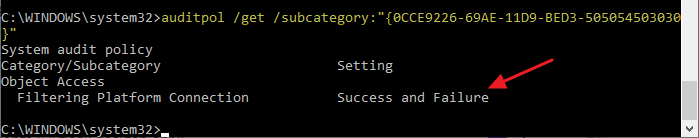
“Filtering Platform Connection” Audit enables automatically?
On some systems, the WFP auditing may get re-enabled automatically in a few minutes. If you run the above “auditpol /get ...” command-line, you may see that audit of “Success and Failure” entries have been switched on automatically (perhaps by some third-party security software installed on the computer.)
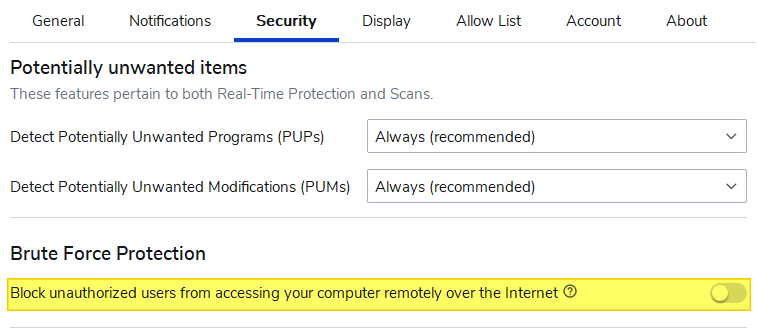
Malwarebytes “Brute Force Protection” setting
If you’re using Malwarebytes Premium and have enabled the Brute Force Protection option in the Security tab, turn the setting off.
If this setting is turned on, it enables WFP “Success and Failure” auditing automatically. Even if you disable auditing manually using auditpol.exe, Malwarebytes re-enables WFP auditing every 4-5 minutes.
Editor’s note: If you need the “Brute Force Protection” turned on and yet want to disable the WFP event logging, you may contact Malwarebytes support to see if a workaround is available.
Once done, re-run the following command from the admin Command Prompt:
auditpol /set /subcategory:"{0CCE9226-69AE-11D9-BED3-505054503030}" /success:disable /failure:disable
This disables the excessive logging of the Windows Filtering Platform (“Filtering Connection Platform”) “Success” and “Failure” events (Event ID 5156, 5157, and 5158).
Alternatively, for diagnostic purposes, you can opt to log only the “Failure” entries using the auditpol.exe command. The “Failure” entries would be significantly less in number when compared to “Success” entries.
As of this blog post, Malwarebyte’s current version is 4.5.11.202 — Update package version is 1.0.57424 — Component package version is 1.0.1716.
One small request: If you liked this post, please share this?
One "tiny" share from you would seriously help a lot with the growth of this blog. Some great suggestions:- Pin it!
- Share it to your favorite blog + Facebook, Reddit
- Tweet it!
This was awesome.
How to do the same for for Event IDs 4688 success 4799 Success?
I really don’t need to know what went right, just what needs attention.