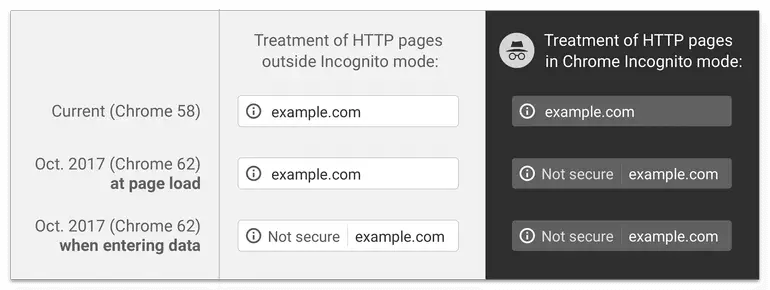
Google has announced that starting with Chrome browser version 62, ‘Not secure’ warnings will be shown for HTTP pages with user input fields and all HTTP pages in incognito mode. Going forward, ‘Not secure’ warning would be shown for all HTTP pages even in normal browsing mode.
Considering Google Chrome’s browser market share which is around 60%, it’s imperative that you enable SSL for your website. Many web hosts provide free SSL certificates issued by LetsEncrypt.
If you’ve employed a reverse-proxy solution for your website, like Sucuri Web Application Firewall (WAF) or Cloudflare, they offer SSL certificates free of cost to you. That’s sufficient for enabling “Partial SSL” or “Flexible SSL”.
Partial/Flexible SSL provides a secure connection between your visitor and your reverse-proxy server (Sucuri, CloudFlare, etc.), but no secure connection between reverse-proxy and your web server. Although you don’t need to have an SSL certificate on your web server, partial SSL is not recommended if you have any sensitive information on your website. Regardless, your visitors still see the site as being HTTPS enabled.
Sucuri & ServerPilot with Linode, DO, Vultr or other:: LetsEncrypt SSL installation
Enabling Full SSL requires enabling SSL on your web server or the hosting server. You can get a free SSL certificate from LetsEncrypt and install it on your hosting server.
I run my website on Linode and is managed by ServerPilot. I followed this excellent guide written by Robert Went — Using LetsEncrypt With Serverpilot. When following Step 2 in that guide, my domain validation could not succeed since I employ Sucuri’s WAF. Here is the full error message I received in the SSH console.
Obtaining a new certificate
Performing the following challenges:
http-01 challenge for winhelponline.com
http-01 challenge for www.winhelponline.com
Using the webroot path /srv/.../public for all unmatched domains.
Waiting for verification...
Cleaning up challenges
Failed authorization procedure. www.winhelponline.com (http-01):
urn:acme:error: unauthorized :: The client lacks sufficient authorization
:: Invalid response from https://www.winhelponline.com/.well-known/acme-challenge/
"
[title]404 Not Found[/title]
IMPORTANT NOTES:
To fix these errors, please make sure that your domain name was
entered correctly and the DNS A/AAAA record(s) for that domain
contain(s) the right IP address.
It’s important to note that your domain records A/AAAA records must point to your web server IP. Only then you can LetsEncrypt can issue the SSL certificate. If on the other hand, if you’re using a reverse-proxy like Sucuri, you must enable the setting to “forward certificate validation” or similar setting so that you don’t block LetsEncrypt’s domain verification attempts.
In Sucuri’s DNS settings page, you don’t have the option to change the A/AAAA settings as they’re locked down, pointing to Sucuri Web Application Firewall’s IP. So I had to open a support case and asked for a solution to this issue.
Solution: Enable “Forward Certificate Validation”
Sucuri support techs enabled the Forward Certificate Validation to Hosting from their end. After 5 minutes or so, I could complete the steps in that tutorial successfully. SSL is enabled on the hosting server, and I can switch on the Full SSL/https setting in my Sucuri WAF dashboard.
For sites connected to Cloudflare, installing SSL on your web server should be a breeze. I manage another website which is already connected to Cloudflare. I didn’t have to change anything in Cloudflare other than verifying the A/AAAA records which were correctly pointing to the web server. The steps in that tutorial worked right away. Domain verification process was successful and got the LetsEncrypt SSL certificate installed without any issues.
One small request: If you liked this post, please share this?
One "tiny" share from you would seriously help a lot with the growth of this blog. Some great suggestions:- Pin it!
- Share it to your favorite blog + Facebook, Reddit
- Tweet it!