Microsoft Malicious Software Removal Tool (MSRT) is a post-infection removal tool which is updated every month and rolled out through the Windows Update channel. Malicious software scanning runs as you install MSRT from Windows Update. You can also initiate scans manually whenever needed by running mrt.exe in the Windows\System32 directory.
What is MSRT and how does it differ from my AV program?
![]()
MSRT is a tool to remove infections from the computer. But it doesn’t monitor your system real-time. Also, it scans for a specific, prevalent malicious software, which amounts to a small subset of all the malicious software that exists today. Whereas the definitions used your antivirus product are vast — containing signatures for all or most of the malware ever released.
MSRT, as a secondary scanner, is useful in finding and removing viruses, worms, and Trojans. It doesn’t detect spyware, nor does it replace your primary antivirus program’s real-time protection.
The MMPC blog announced that out of the 500 million devices scanned every month, the MSRT identified and removed malicious programs from 1 to 2 million machines, even on those devices running antivirus software. The effectiveness of MSRT as a secondary scanner made Microsoft include “Windows Defender – Limited Periodic Scanning” feature into Windows 10.
Practically speaking, if your original antivirus software is always kept updated and its real-time protection is working fine, MSRT won’t find anything in the vast majority of cases.
MSRT runs in Windows 10, Windows 8.1, Windows Server 2012 R2, Windows 8, Windows Server 2012, Windows 7, Windows Vista, or Windows Server 2008 systems. Microsoft releases an updated version of MSRT on the second Tuesday of each month.
So, from Windows 10’s perspective, if you’re using a 3rd party antivirus solution in Windows 10, Limited Periodic Scanning (when turned on) provides an additional layer of defense. MSRT adds a 3rd layer of this defense, but the automatic scans occur once a month; when Microsoft pushes the latest version of MSRT via Windows Update. And, with Windows Defender Offline integrated into Windows 10, the Operating System is fortified to a greater level.
Running a scan using MSRT
Press WinKey + R to launch the Run dialog. Type mrt.exe and hit ENTER
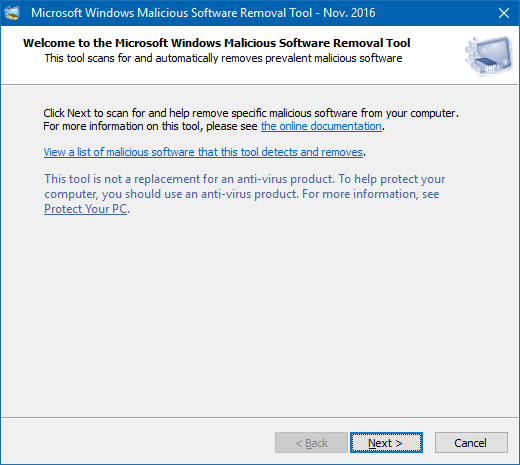
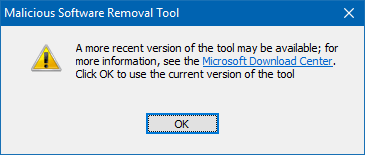
If the version of MRT.exe in your system is older than 60 days, taking the current system date/time into account, MSRT suggests you download the latest version of the tool.
In the “Welcome to the Microsoft Malicious Software Removal Tool,” screen, there is a link to view the list of malicious software this tool removes. Click the link if you want to see the list. Selecting an item in the list box opens the corresponding virus information page at the Microsoft site.
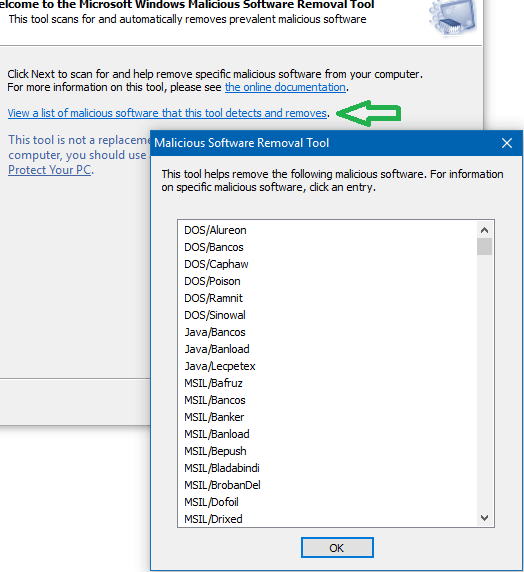
It’s worth noting that most of the malicious software listed there are categorized as alert level “Severe” or “High”.
Click Next to proceed.
Choose a type of scan: Quick scan, Full scan or a Customized scan. Customized scan is used to scan a specific folder in addition to Quick scan. Full scan took extremely long time to complete on my production system.
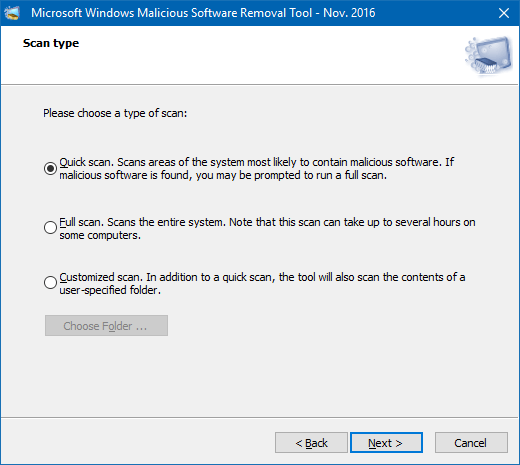
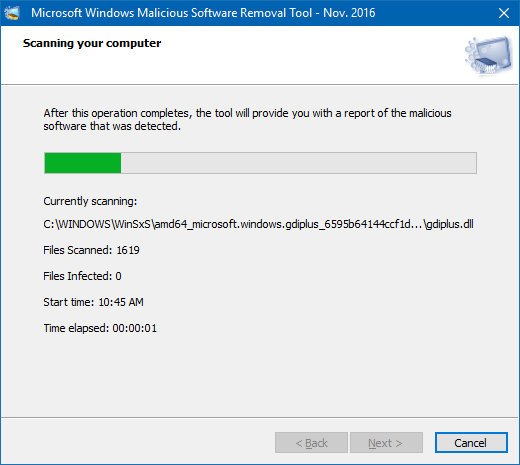
Microsoft’s documentation says “The tool cannot remove malicious software that is not running.” It’s unclear if the statement applies even if one performs a full scan.
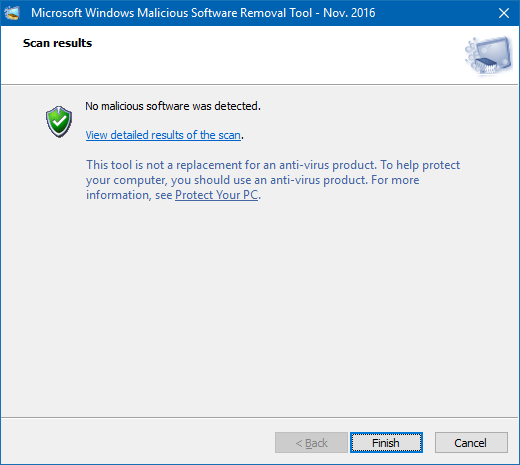
Once the scan completes, it shows you the results immediately. The results are also logged to the file “C:\Windows\Debug\mrt.log”. After each scan, MSRT records the following info to the log file.
Microsoft Windows Malicious Software Removal Tool v5.42, November 2016 (build 5.42.13202.0)
Started On Wed Nov 09 10:18:52 2016
Engine: 1.1.13202.0
Signatures: 1.231.682.0
Run Mode: Interactive Graphical Mode
Successfully Submitted Heartbeat Report
Microsoft Windows Malicious Software Removal Tool Finished On Wed Nov 09 11:19:58 2016
Return code: 0 (0x0)“Run Mode” would say “Scan Run From Windows Update” if the scan was initiated automatically from Windows Update.
MSRT supports these command-line arguments:
/Q or /quiet - quiet mode; if set, no UI is shown
/? or /help - displays usage information
/N - detect-only mode
/F - force full scan
/F:Y - same as above, but automatically clean infected files.
Scans initiated from Windows Update run in quiet mode by default. But, if MSRT finds a malicious software, it sends a balloon or toast notification suggesting the user run a full scan.
Disable MSRT from sending Telemetry Report to Microsoft
Woody Leonhard also found out that, as of August 2016, MSRT submits HeartBeat or Telemetry report to Microsoft — as seen in the mrt.log which contains the line “Successfully Submitted Heartbeat Report”. Microsoft, however, provides a registry method in article Deployment of the Microsoft Windows Malicious Software Removal Tool in an enterprise environment to stop MSRT from reporting the infection to Microsoft.
How can I disable the infection-reporting component of the tool so that the report is not sent back to Microsoft?
An administrator can choose to disable the infection-reporting component of the tool by adding the following registry key value to computers. If this registry key value is set, the tool will not report infection information back to Microsoft.
Start the Registry Editor (regedit.exe), and go to the following key:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT
Create a DWORD value named “DontReportInfectionInformation”, and set its value data to 1.
For detailed information on MSRT, check out Microsoft article: MSRT helps remove specific, prevalent malicious software from computers.
Also see the recent MMPC blog post: MSRT November 2016: Unwanted software has nowhere to hide in this month’s release. MSRT can now (Nov 2016 update) remediate systems infected by Soctuseer malware. Since September 2016, Soctuseer has infected 1.2 million systems.
Microsoft Safety Scanner
Microsoft has another standalone virus and malware scanner, named Microsoft Safety Scanner (free). MSS has an interface that’s similar to MSRT, but it’s more comprehensive than MSRT. The standalone tool is bigger in size, and it can scan and remove viruses, spyware, and other malicious software.
Even though MSS uses the same set of virus and malware definitions used by Microsoft Security Essentials and Windows Defender, MSS expires 10 days after you download it and you can’t delta update the definitions as it’s a single executable. To rerun a scan with the latest anti-malware definitions, you’ll need to download and run the Microsoft Safety Scanner again. It logs the scan results to the file “C:\Windows\Debug\msert.log”
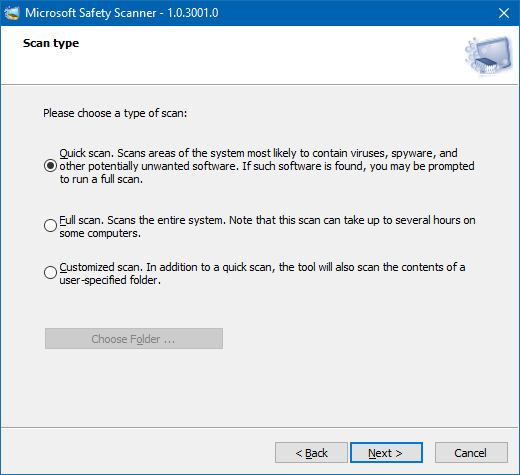
The system requirements page of MSS states Windows 7 is required, but it runs just fine on Windows 10 as well.
So, which scanner should I use?
If too many scanner options provided by Microsoft have left you baffled, note that MSRT is intended to be run silently and automatically via WU; whereas MSS is an on-demand scanner which the user needs to download whenever they need to run a thorough scan.
Likewise, Windows Defender Offline (WDO) is started on-demand by the user, or when Defender suggests you run an offline scan when it finds a deep-rooted malware infection in the system which can’t be removed when Windows is running. On the other hand, Limited Periodic Scanning in Windows 10 requires no user intervention.
One small request: If you liked this post, please share this?
One "tiny" share from you would seriously help a lot with the growth of this blog. Some great suggestions:- Pin it!
- Share it to your favorite blog + Facebook, Reddit
- Tweet it!
Have you ever looked at the MSS license agreement? It has clause that say one may only use it to “design, develop and test your programs”! Funny, isn’t it?
@Fleet Command: Haven’t looked at the license agreement.. but wondering why would they include that clause. Will read it fully, later.
@RS: I believe it is just a copy and paste error. But it prevents me from using MSS in workplace.
I ran a full scan… it seemed to take forever. accidently shut off the computer during the scan…I cant find the scan or its result. first I ran a quick scan… no malicious files. then I ran the full scan… after 5 hours(still was running) it found 2 mal files. What can I do to locate those files